

Advanced OAuth Security

What you'll learn
- How to leverage the advanced OAuth specifications for high-security applications
- Learn the details of the FAPI specifications, including the FAPI Security Profile and FAPI Message Signing
- Learn the purpose of JAR, JARM, MTLS, DPoP, HTTP Signatures, and Non-Repudiation
- How to apply HTTP Message Signing and JWTs to achieve non-repudiation for every role in an OAuth exchange
Explore related topics
Coding Exercises
This course includes our updated coding exercises so you can practice your skills as you learn.
See a demo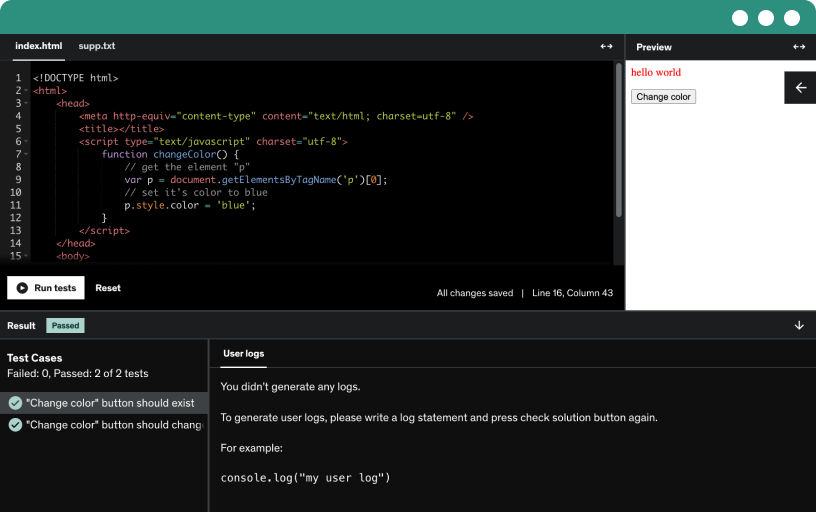
Course content
- Intro to this Course1:17
- Intro to Part 10:33
- Review of the Authorization Code Flow3:30
In this lesson, we'll review the authorization code flow and summarize the roles in OAuth. We'll discuss how a user, device, and application work together to access resources at an API using access tokens. We will also examine how the authorization code flow starts with the user logging in to the application and how the application then exchanges an authorization code for an access token. Understanding these roles and the flow will set the stage for the rest of this course.
- Front Channel vs Back Channel2:27
Learn about the front channel and back channel in OAuth and how they differ in different environments such as server side apps, single page apps, and mobile apps. Understand the role of the browser, the client, and HTTP library in these processes and how attackers can potentially manipulate data in the front channel.
- Front Channel vs Back Channel
- Security Goals1:27
In this lesson, we'll learn about the different categories of threats that extensions can protect against, including authorization, authentication, and session integrity. We'll also explore how to ensure that access and ID tokens are secure and how to prevent attackers from tricking users into logging in as someone else or using someone else's access token.
- Attacker Model4:25
This lesson will cover different types of attackers and their capabilities in the context of advanced OAuth security. It will also discuss limitations and assumptions, such as correctly functioning TLS and JWKS URLs, and the assumption that secret keys are kept secret. We'll delve into specific types of attackers, including web attackers, network attackers, and attackers with compromised endpoints, and will discuss how to protect against them in the authorization request process.
- Protecting the OAuth Flow4:30
In this lesson, we will recap the end to end OAuth flow and show where all the specs and elements in the future lessons relate to the overall flow. We'll cover topics such as adding integrity to front-channel requests, preventing authorization code injection, using sender constrained tokens to ensure that only the intended recipient can use an access token, and more. We will also explore different options for client authentication and methods to validate access tokens at the resource server.
- Security in OAuth 2.0
- Intro to Part 20:32
- Authorization Code Injection Attacks3:52
In this lesson, we'll learn about authorization code injection attacks, a type of attack that occurs when an attacker injects an authorization code into a browser performing an authorization code exchange. This can have serious consequences, such as a victim being logged into the attacker's account or the attacker being logged into the victim's account. We will also explore measures to protect against these types of attacks, including the use of PKCE to tie a particular request with the resulting authorization code. This attack is relevant to all types of clients, including public and confidential ones.
- How PKCE Prevents Authorization Code Injection Attacks4:42
In this lesson, we'll go through the authorization code flow to understand how an authorization code attack occurs and how PKCE prevents the attack from succeeding. We will see how PKCE associates a secret code with a particular user session, and how it uses this secret code to ensure that the correct authorization code is exchanged for an access token. By the end of the lesson, you will have a deeper understanding of how authorization code attacks work and how to protect against them.
- Calculate a PKCE code verifier and code challenge
- History of PKCE3:34
This lesson discusses the history and evolution of PKCE in OAuth 2.0, and how its used evolved over the years from mobile apps to JavaScript apps to now be used by every type of OAuth client.
- PKCE
- Authorization Server Mixup Attacks5:04
In this lesson, we'll explore the concept of authorization server mix-up attacks, in which an attacker controls one of the authorization servers that a client may use. We will go through the process step by step, explaining how the attack works and how the attacker can ultimately gain access to an authorization code and exchange it for an access token. We will also discuss the technique to prevent this type of attack.
- Preventing Mixup Attacks with the Authorization Server Issuer Identifier3:27
In this lesson, we'll learn about the Authorization Server Issuer identifier (iss), which helps prevent the "authorization server mixup attack." This mechanism involves the server adding a new parameter, "iss," to the authorization response, which tells the client which authorization server is sending the response.
- Mixup Attacks
- The Problems with Starting in the Front Channel3:23
In this lesson, we will discuss the potential issues that arise when starting an OAuth flow in the front channel, including the risk of the user or other software modifying or intercepting the request, the length and sensitivity of data sent in the front channel, and the lack of guarantee of authenticity for the client making the request.
- Avoiding the Front Channel with Pushed Authorization Requests3:29
In this lesson, we'll explore an extension to OAuth called Pushed Authorization Requests (PAR) which makes the authorization process more secure by avoiding the use of the front channel. We will discuss how this extension works and how it can be used with different types of clients, including web servers, mobile apps, and single page apps. We will also delve into the concept of client authentication and how it can be used to add an extra layer of security to the authorization process.
- Pushed Authorization Requests
- Client Authentication in OAuth2:03
In this lesson, we'll learn about the problems with the simpler "client secret" model of client authentication in OAuth, and explore the more secure forms of client authentication available, including Private Key JWT and Mutual TLS.
- MTLS as Client Authentication5:11
In this lesson, we will discuss Mutual TLS as a form of client authentication, in which the client presents its own certificate to the server when establishing a connection. We will also discuss the use of Mutual TLS with reverse proxies and how it can be used to provide identity verification of clients.
- Private Key JWT as Client Authentication3:25
In this lesson, we will learn about using a Private Key JWT for client authentication in OAuth and OpenID Connect. We will use a JSON web token (JWT) signed with the client's private key and include certain required claims to authenticate the client to the authorization server. This method is simpler and easier to deploy compared to Mutual TLS.
- Back Channel
- Intro to Part 40:38
- Additional Requirements for Access Token Validation5:49
In this lesson, we will discuss the additional steps that resource servers must take when validating tokens. This includes verifying the validity, integrity, expiration, and revocation status of access tokens. We will also discuss the different ways in which access tokens can be transmitted, as well as the different options for checking a token's revocation status.
- The Problem with Bearer Tokens3:53
In this lesson, we will discuss the concept of Bearer Tokens and how they became the dominant form of access tokens in OAuth. We will also discuss the security risks associated with bearer tokens and the idea of using sender constraining as a solution to improve security.
- MTLS for Sender-Constrained Access Tokens4:17
In this less we'll discuss Mutual TLS as a way to bind access tokens to a client certificate. We'll cover how Mutual TLS can be deployed with a PKI model or self-signed certificates, and how it can be used to bind access tokens to client certificates in OAuth. This lesson also covers the role of the resource server in recognizing and validating client certificates and access tokens, and the implications of using Mutual TLS with public clients.
- DPoP for Sender-Constrained Access Tokens5:41
This lesson covers DPoP (Demonstrating Proof of Possession), an alternative to Mutual TLS that works at the application layer. It involves the use of JSON Web Tokens to prove possession of a key and establish a link between an access token and the key used to request it. This lesson covers the required and optional claims that must be included in a DPoP proof, as well as how to create and sign the proof. The lesson also discusses the use of nonces to ensure that the client has recently created the proof.
- Access Tokens
- Intro to Non-Repudiation1:40
- Signing Authorization Requests (JAR)6:05
In this lesson, we'll explore how to ensure non-repudiation in the OAuth authorization request. While Pushed Authorization Requests solves the dangers of sending the request details in the front channel, we need something extra to add non-repudiation. We'll introduce the use of JSON Web Tokens to provide a signature for the authorization request to prove that it was actually made by the client.
- Signing Authorization Responses (JARM)3:10
This lesson focuses on adding non-repudiation to the response the authorization server sends to the client using the "JWT-Secured Authorization Response Mode" (JARM). We'll discuss the use of JARM in the context of the various response modes used in OAuth and OpenID Connect.
- JAR and JARM
- Signing Token Introspection Responses4:45
In this lesson we'll focus on the JWT Response for OAuth Token Introspection specification, which enables a resource server to request a JWT from the Authorization Server as part of the token introspection process. This JWT contains information about the token being validated, as well as a signature for non-repudiation.
- Signing All Resource Requests4:41
In this lesson, we'll introduce HTTP signatures, a new IETF draft for signing HTTP requests and responses. We'll focus on how HTTP Signatures can be applied in the context of FAPI to add non-repudiation to the client's resource request.
- Signing All Resource Responses2:14
In this lesson we'll apply HTTP Signatures to the resource server's response, so the client can ensure non-repudiation of the responses it gets from the API.
- HTTP Signing
- Summary of Non-Repudiation0:51
- Congratulations!1:57
Requirements
- A basic understanding of HTTP requests, responses, and JSON
- An understanding of the basics of OAuth flows, especially the Authorization Code Flow
- Familiarity with JSON Web Tokens (JWT)
Description
Certain applications need a higher level of security compared to what is part of the core OAuth 2.0 specifications. This course will guide you through the details of FAPI, a set of extensions of OAuth 2.0 that provide additional layers of security throughout the OAuth flows.
This course covers the extensions of OAuth developed by the OAuth Working Group at the IETF as well as the OpenID Foundation, including:
PKCE
Authorization Server Issuer Identifier (iss)
Pushed Authorization Requests (PAR)
Mutual TLS (MTLS)
Private Key JWT
Demonstration of Proof of Possession (DPoP)
JWT Response for OAuth Token Introspection
JWT-Secured Authorization Requests (JAR)
JWT-Secured Authorization Response Mode (JARM)
HTTP Signatures
This course is for you because...
You've got a solid understanding of the basics of OAuth, and
You're looking to take your knowledge to the next level
You want to ensure the systems you're building are up to the industry standards in security
You want to deepen your understanding of application security and become a technical leader
Prerequisites
An understanding of HTTP requests, responses, and JSON
A basic understanding of JSON Web Tokens (JWT)
Familiarity with the OAuth authorization code flow
The content is divided into five parts, beginning with and overview of the OAuth authorization code flow, an overview of the security goals set out by FAPI and related extensions, as well as a description of the types of attacks we are concerned about protecting against. Part two focuses on securing the front channel, where we'll discuss authorization code injection attacks, PKCE, authorization server mixup attacks, and using Pushed Authorization Requests. Part three focuses on the back channel, and discusses the differences between Mutual TLS and Private Key JWT for client authentication. Part four is all about proof-of-possession (sender-constraining) access tokens using Mutual TLS and DPoP. Part five discusses how to achieve non-repudiation throughout each leg of the OAuth flow.
Who this course is for:
- Software architects, application developers, or technical decision makers
- API developers who want to better secure their APIs
- Developers and software architects working in high-security fields working with financial or medical records